- 26 Nov 2023
- Print
- DarkLight
Splunk Integration
- Updated on 26 Nov 2023
- Print
- DarkLight
The Bot Defender App for Splunk allows you to add prebuilt dashboards to help you visualize your Bot Defender logs. These dashboards allow you to see key data points and identify potential spikes in activity across all logs from within Splunk.
Configuring the Integration
- Configure a Splunk integration as specified here
- From within your Splunk instance's App menu, click on the Find More Apps link.
- On the resulting Browse More Apps page, search for
PerimeterX. - Locate the
PerimeterX Bot Defender App for Splunkin the results. - Click the Install button.
- Login to your Splunk.com account to download and install the App.
PerimeterX Bot Defender App for Splunk supports obtaining data from a specific index and events of a specific source type. As an optional step, you can choose to configure your Splunk instance to index the data under a custom index and with a specific source type.Validating App Installation
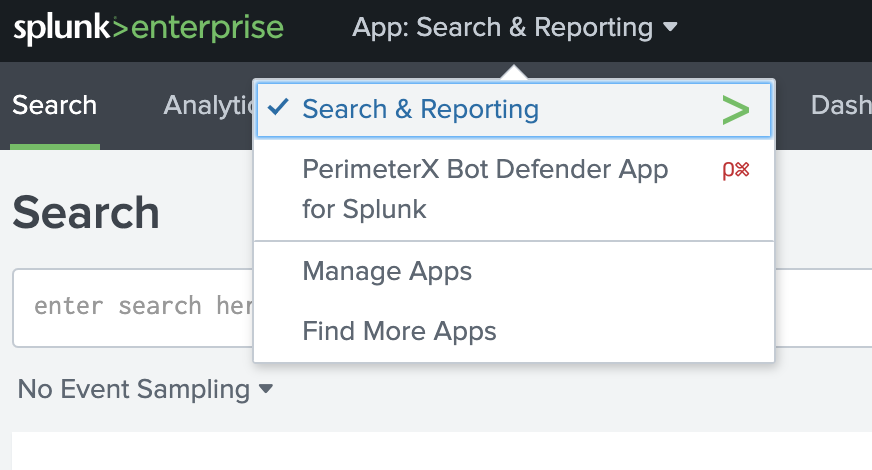
- Login to your Splunk instance
- Click on the App menu and confirm that the
PerimeterX Bot Defender App for Splunkis listed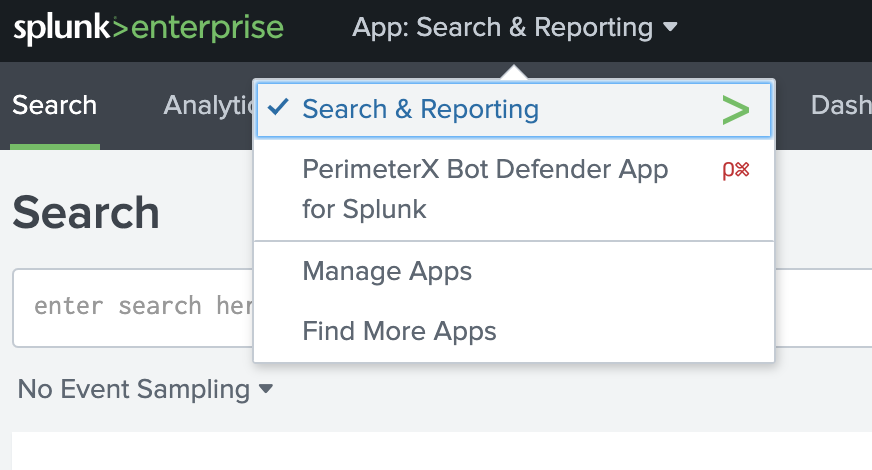
- Click on the
PerimeterX Bot Defender App for Splunkmenu item to load the App.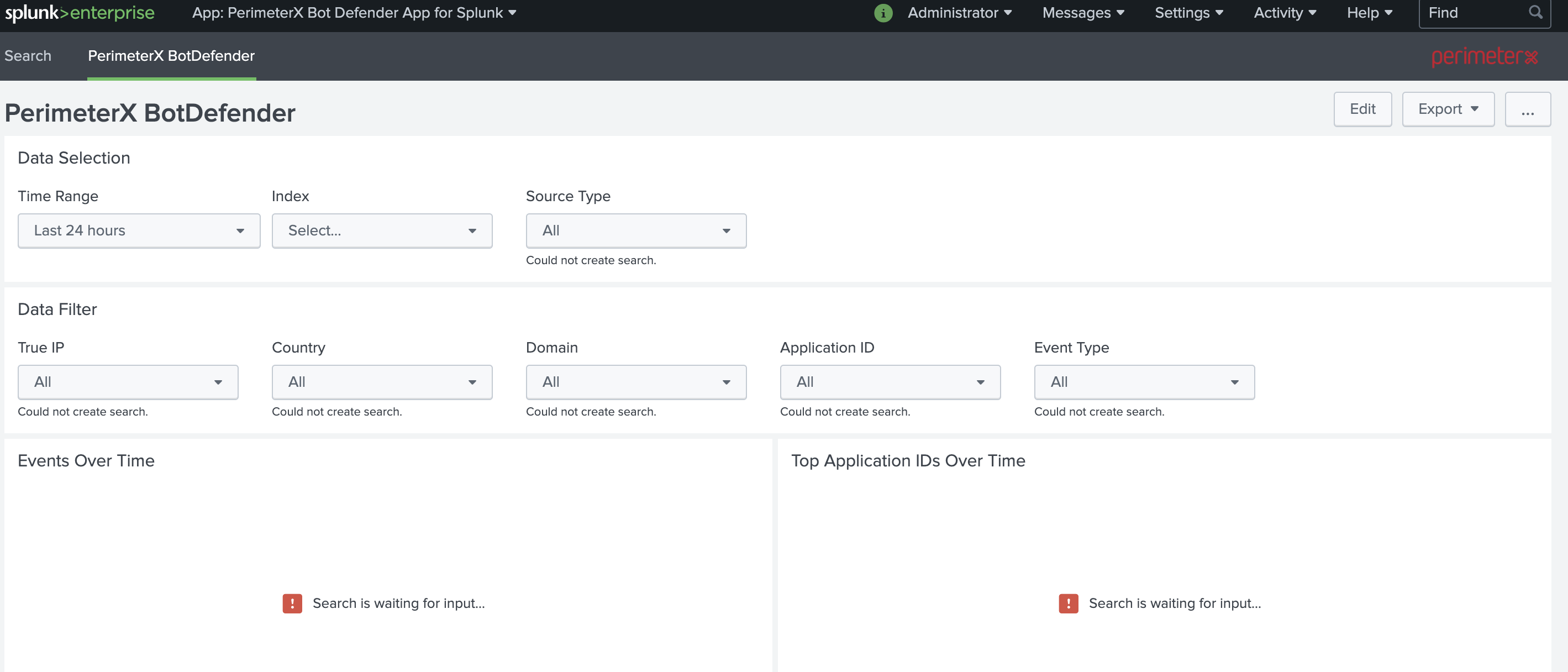
Using the Application
Once PerimeterX support has confirmed that the integration is complete, you should begin receiving data into your Splunk instance. Once data begins populating into your Splunk, you can begin using the PerimeterX Bot Defender App for Splunk.
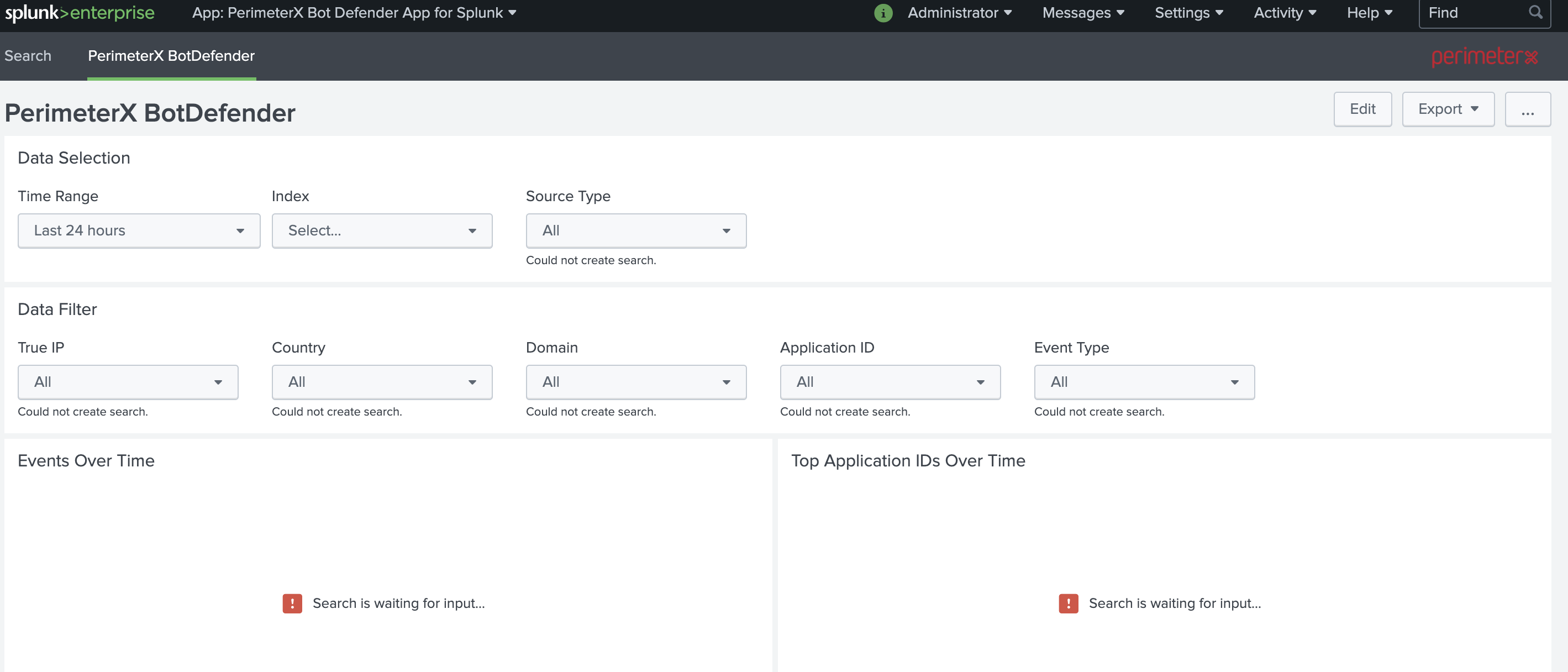
When you access the PerimeterX Bot Defender App for Splunk, you will be presented with the dashboard for your data. The panels will be blank until you have at least selected index from the Index drop down. Once that is selected, the data panels will populate with data. You can additionally choose to select the sourc etype specified for your Bot Defender data if you added a custom sourcetype for these logs.
In addition, the Data Filter drop downs allow you to filter the graphs by selected fields. Below is an example of the App with no filtering and the panels populated